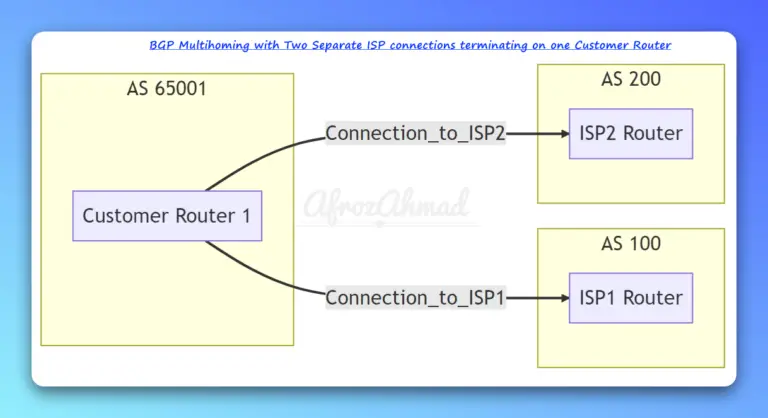
The backbone of inter-Autonomous System (AS) communication on the internet relies heavily on External Border Gateway Protocol (eBGP). As networks evolve, so do the best practices and methods for configuring, securing, and automating eBGP peering. This updated guide dives into the fundamentals of eBGP, common peering scenarios, and introduces modern approaches to ensure robust and resilient internet connectivity.
Understanding eBGP Peering
eBGP allows routers in different Autonomous Systems (AS) to exchange routing information. This is fundamental for connecting your network to the internet or peering with other organizations. Key characteristics include:
- Administrative Distance (AD): For eBGP routes, the default administrative distance on Cisco devices is 20, making them highly preferred over routes learned via IGPs like OSPF (110) or EIGRP (90/170).
- Default Time-to-Live (TTL): By default, eBGP packets are sent with a TTL of 1. This strict check ensures that eBGP sessions are only established between directly connected routers, preventing unexpected peering across multiple hops and enhancing security.
Handling Non-Directly Connected eBGP Neighbors
While the default TTL of 1 promotes security, there are common scenarios where eBGP neighbors are not directly linked. This includes peering over loopback interfaces for redundancy or across an intermediate transit network. In such cases, the default TTL must be adjusted.
There are three primary methods to manage the TTL for eBGP sessions:
1. Peering with Loopback Interfaces (update-source and ebgp-multihop)
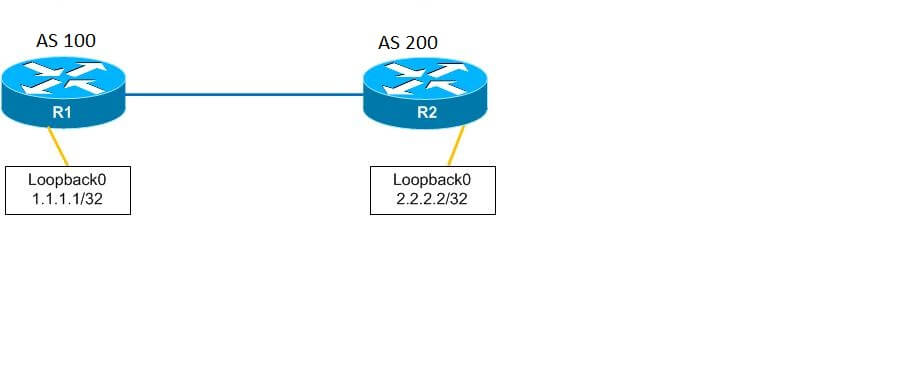
Peering eBGP over loopback interfaces offers significant advantages, primarily increased resilience. If a physical interface goes down, but connectivity to the loopback is still available through another path, the BGP session remains active. This requires two specific commands:
neighbor [IP] update-source loopback0: This command tells BGP to use the specified loopback interface’s IP address as the source IP for BGP packets, rather than the directly connected physical interface.neighbor [IP] ebgp-multihop [TTL value]: Since the loopback interface is not directly connected, the BGP packets need to traverse at least one additional hop (to reach the neighbor’s loopback). This command increases the TTL value in the IP packet header, allowing it to span multiple router hops. The `TTL value` should be set to at least 2 for directly adjacent routers peering via loopbacks, or higher if more intermediate routers are involved.
Example Configuration (Cisco IOS-XE):
Suppose Router R1 (AS 100, Loopback0: 1.1.1.1) and Router R2 (AS 200, Loopback0: 2.2.2.2) want to establish eBGP peering using their respective loopbacks.
# Configuration for R1 (AS 100)
R1(config)#router bgp 100
R1(config-router)#neighbor 2.2.2.2 remote-as 200
R1(config-router)#neighbor 2.2.2.2 update-source Loopback0
R1(config-router)#neighbor 2.2.2.2 ebgp-multihop 2 # Allows 2 hops (R1 physical -> R2 physical -> R2 loopback)
R1(config-router)#exit
# Configuration for R2 (AS 200)
R2(config)#router bgp 200
R2(config-router)#neighbor 1.1.1.1 remote-as 100
R2(config-router)#neighbor 1.1.1.1 update-source Loopback0
R2(config-router)#neighbor 1.1.1.1 ebgp-multihop 2 # Allows 2 hops (R2 physical -> R1 physical -> R1 loopback)
R2(config-router)#exit
In this scenario, `ebgp-multihop 2` is used because the BGP packet from R1’s loopback needs to travel to R1’s physical interface (1st hop), then across the link to R2’s physical interface, and finally to R2’s loopback interface. A value of 2 is sufficient for directly connected routers using loopbacks for peering.
2. Bypassing Direct Connectivity Check (disable-connected-check)
The disable-connected-check command instructs BGP to ignore the default requirement that an eBGP neighbor must be directly connected. This is useful in specific multi-hop scenarios, particularly when a transit router exists between two eBGP peers and the TTL is being handled by other means or if the BGP next-hop is not directly connected but is reachable via an Interior Gateway Protocol (IGP).
R2(config-router)#neighbor 1.1.1.1 disable-connected-check
Note: This command, while functional, provides less granular control over the TTL than `ebgp-multihop` and should be used with caution, as it can potentially weaken the default security posture.
3. Enhancing Security with TTL Security (ttl-security hops)
The ttl-security hops command is a robust security feature that both enables multi-hop eBGP and protects against IP spoofing and certain DoS attacks. It leverages the Generalized TTL Security Mechanism (GTSM).
R2(config-router)#neighbor 1.1.1.1 ttl-security hops 2
When enabled, BGP expects incoming packets from the specified neighbor to have a TTL value within a specific range. Specifically, it calculates a minimum expected TTL based on the configured `hops` value (255 – hops + 1). If an incoming BGP packet’s TTL is below this calculated minimum, it’s silently discarded. This prevents attackers from injecting BGP messages with spoofed source IPs or low TTL values, which would typically be dropped by intermediate routers.
For two directly connected routers peering via loopbacks, `ttl-security hops 2` would configure the router to expect a TTL of 254 or 255 (255 – 2 + 1 = 254). This is generally the recommended approach for secure multi-hop eBGP peering.
Modern eBGP Deployments and Best Practices
Enhanced BGP Security
Beyond TTL security, robust eBGP deployments incorporate additional security layers:
- MD5 or TCP Authentication Option (TCP-AO): Cryptographically authenticates BGP packets, preventing unauthorized or spoofed BGP messages. TCP-AO is the modern successor to MD5, offering stronger algorithms and key rotation.
- Route Origin Validation (ROV) with RPKI: Cryptographically verifies that an Autonomous System is authorized to originate specific IP prefixes, preventing accidental or malicious route hijacks.
- BGP Flowspec: Allows the dynamic distribution of traffic filtering rules (e.g., to mitigate DDoS attacks) through BGP, enabling rapid response to security incidents.
eBGP in Data Centers and Cloud Environments
eBGP plays a critical role in modern network architectures:
- EVPN-VXLAN Underlay/Overlay: In data centers using EVPN-VXLAN, eBGP is commonly used as the underlay routing protocol to establish reachability between VTEPs, and also to distribute EVPN routes for overlay network services.
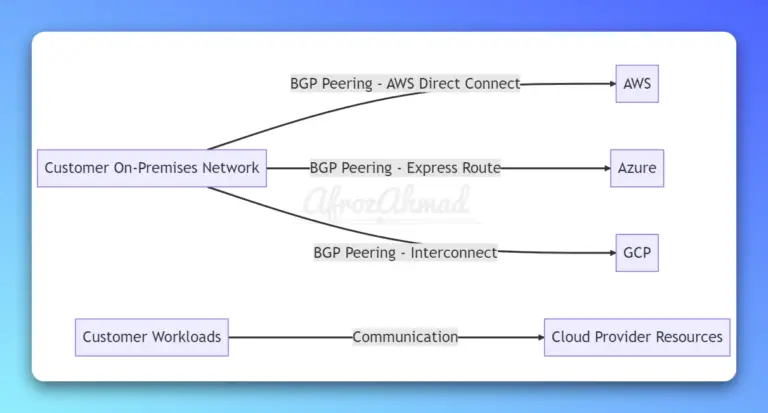
- Cloud Connectivity: Major cloud providers like AWS (Direct Connect) and Azure (ExpressRoute) primarily use eBGP for connecting customer on-premises networks to their cloud infrastructure, enabling scalable and resilient hybrid cloud deployments.
eBGP and SD-WAN
In Software-Defined Wide Area Network (SD-WAN) solutions, eBGP is often used at the edge to peer with internet service providers or other external networks. While the SD-WAN orchestrator manages internal policies and overlays, eBGP ensures traditional external connectivity, often with dynamic path selection influenced by application requirements and link performance.
Automating eBGP Peering Configuration
Manual configuration of BGP can be error-prone and time-consuming, especially in large, dynamic networks. Network automation tools are essential for managing eBGP at scale:
- Configuration Management Tools:
- Ansible: Popular for its agentless nature, using modules (e.g., `cisco.ios.ios_bgp`) to configure BGP on various platforms.
- Nornir: A Python-based automation framework that provides a flexible inventory and task runner, often used with libraries like Netmiko or Scrapli for device interaction.
- NAPALM: A Python library that provides a unified API to interact with different network device operating systems, simplifying multi-vendor BGP automation.
- Infrastructure as Code (IaC): Defining BGP configurations in version-controlled text files (e.g., YAML, Jinja2 templates) and deploying them through CI/CD pipelines ensures consistency and enables rollbacks.
- RESTCONF/gNMI: Modern network devices support programmatic interfaces like RESTCONF (for configuration) and gNMI (for streaming telemetry), enabling direct API-driven BGP configuration and state management.
Observability and Monitoring for eBGP
Real-time visibility into eBGP session states and routing updates is crucial for network stability. Modern observability platforms leverage:
- Streaming Telemetry (gNMI/gRPC): Provides high-frequency, granular data streams of BGP neighbor states, prefix counts, and session events, offering a significant upgrade over traditional polled methods like SNMP.
- Network Monitoring Tools: Integrate with telemetry data to visualize BGP topology, alert on session flaps, route withdrawals, or unexpected prefix changes.
- AIOps: Leveraging Artificial Intelligence and Machine Learning to detect anomalies in BGP behavior, predict potential issues, and assist in root cause analysis.
Conclusion
eBGP remains a cornerstone of internet routing, but its deployment has evolved significantly since 2011. While the fundamental principles of TTL management and peering remain, modern best practices emphasize enhanced security, automation for consistency and scalability, and advanced observability for proactive management. By adopting these contemporary approaches, network engineers can build more resilient, secure, and manageable inter-AS connections.