BGP Reachability
BGP Reachability ================= R1 | | | R2—FR CLOUD—R6 | | | R5 Here in the above scenario R1 and R2 both connected to R6 via Frame-relay cloud and OSPF area 0 is running between all of them, and…
BGP Reachability ================= R1 | | | R2—FR CLOUD—R6 | | | R5 Here in the above scenario R1 and R2 both connected to R6 via Frame-relay cloud and OSPF area 0 is running between all of them, and…
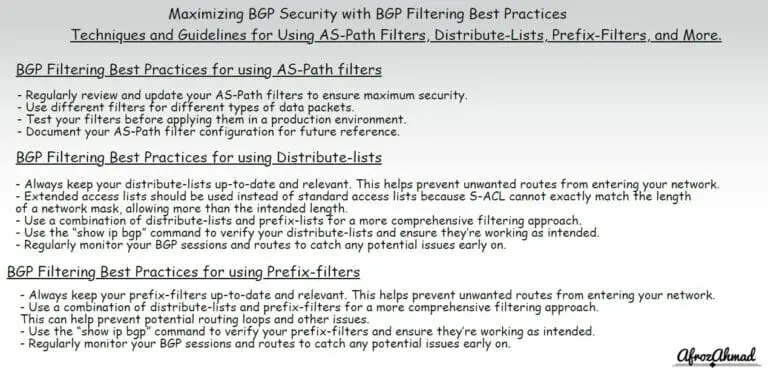
BGP Filtering Best Practices: Techniques and Guidelines for Using AS-Path Filters, Distribute-Lists, Prefix-Filters, and More.
BGP Default Route Origination ============================= We can originate default route to specific BGP neighbor through route bgp [AS No.] neighbor [ip address] default-originate Note:-By doing this the Default route is originated to the BGP peer along with the other routes…
Today while i was doing lab i was stuck in the scenario where i have to do unequal cost load balancing in the eigrp domain.After many hours i finally got the desired result , thought of sharing this , kindly…