BGP, or Border Gateway Protocol, is one of the core protocols that make the internet function. It enables communication between different Autonomous Systems (AS) by exchanging routing information between them.
However, as with any technology, BGP is also vulnerable to a range of security threats, including route hijacking, route leaks, and DDoS attacks, which can disrupt internet connectivity, cause downtime, or result in data breaches.
In this article, we will discuss 14 BGP Security best practices. These best practices will help ensure that your network is protected from potential attacks and breaches.
Before we dive in, make sure you have read through my previous BGP posts.
- What is BGP in Networking
- BGP Message Types
- BGP States
- How to advertise routes in BGP – 5 Simple Techniques
- eBGP vs iBGP
- What is BGP Regular Expression
Let’s get started.
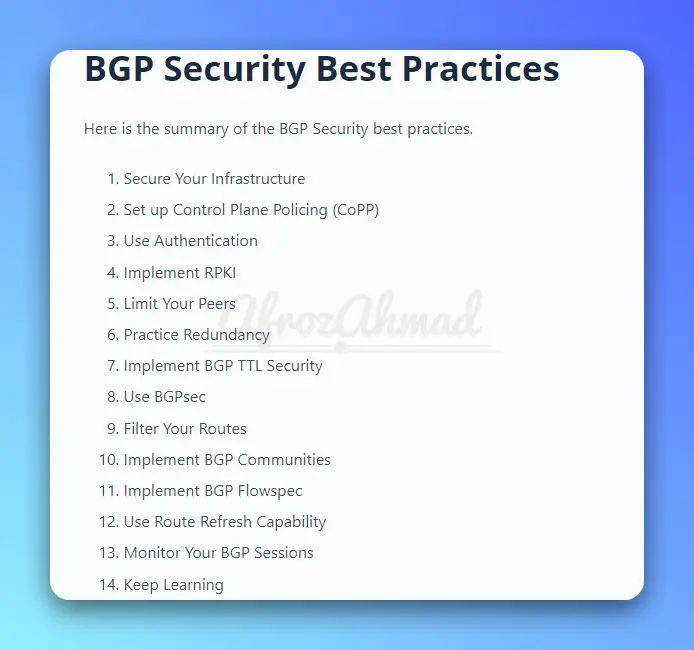
BGP Security Best Practices
Here is the summary of the BGP Security best practices.
- Secure Your Infrastructure
- Set up Control Plane Policing (CoPP)
- Use Authentication
- Implement RPKI
- Limit Your Peers
- Practice Redundancy
- Implement BGP TTL Security
- Use BGPsec
- Filter Your Routes
- Implement BGP Communities
- Implement BGP Flowspec
- Use Route Refresh Capability
- Monitor Your BGP Sessions
- Keep Learning
Let’s dive into each of the BGP Security best practices.
1. Secure Your Infrastructure
The first step towards securing your BGP network is to protect the infrastructure that supports it. Ensure that all your network devices, such as routers, switches, and firewalls, are up-to-date with patches and firmware and that they have strong passwords, authentication mechanisms, and access controls.
They should also be in a gated facility with secured access. You should also monitor your network for unusual traffic patterns, anomalies, and unauthorized access attempts.
2. Set up Control Plane Policing (CoPP)
The second step is to secure the router’s control plane running BGP.
Control Plane Policing (CoPP) is a critical security measure for network operators that help mitigate malicious activity on their networks. By setting up control plane protection, you can ensure that only authorized traffic is allowed to pass to the router’s control plane or the route processor. Additionally, CoPP can help protect your routers from being overloaded and crashing due to sudden spikes in traffic or other malicious activities.
Setting up CoPP involves configuring Cisco IOS commands that determine what types of traffic or protocols (such as BGP, OSPF, MPLS, RSVP, etc.) are allowed in and out of your router’s control plane. You will also need to specify the rate at which packets are sent, as well as the action is taken when certain thresholds are reached with regards to incoming/outgoing traffic.
All major vendors, including Cisco, Nokia, Juniper, etc, offer CoPP.
By taking the time to properly set up Control Plane Policing (CoPP), you can rest assured that your systems remain secure and protected against malicious actors who may try to take advantage of vulnerable points on your network. This simple yet powerful security measure can go a long way toward ensuring the safety and reliability of your systems!
3. Use Authentication
BGP allows peers to exchange routing information without authentication by default. However, this can lead to man-in-the-middle attacks, where an attacker intercepts and alters the traffic between two peers. To prevent this, you should enable authentication mechanisms such as MD5 or TCP-AO to verify the identity of your peers and ensure that only authorized parties can participate in the BGP session.
4. Implement RPKI
RPKI (Resource Public Key Infrastructure) is a mechanism for validating the origin of BGP routes. It involves using digital certificates to verify that a particular AS is authorized to originate a specific prefix. By implementing RPKI, network operators can prevent route hijacking attacks and ensure the integrity of the routing system.
5. Limit Your Peers
Limiting the number and type of peers that you connect to can reduce your exposure to security risks. You should only peer with trusted organizations that have good reputations and security practices. You should also use access-lists or prefix-lists to limit the prefixes that you exchange with your peers and to ensure that you do not act as a transit AS for unauthorized traffic.
6. Practice Redundancy
Practicing redundancy in your BGP infrastructure can ensure that your network stays operational even in case of failures or attacks. You should have multiple paths, multiple peering points, and multiple providers to ensure that traffic can be rerouted quickly and efficiently. You should also use mechanisms such as BGP Multi-Homing or AnyCast to distribute your traffic and improve your performance and resilience.
7. Implement BGP TTL Security
BGP TTL Security is a mechanism for preventing BGP packets with a low TTL value from being forwarded. This practice can help to prevent DDoS attacks that exploit BGP by sending a large number of packets with a low TTL value to overload the routing system. However, it is important to balance the need for security with the need for efficient routing.
8. Use BGPsec
BGPsec is a protocol extension defined in RFC 8205 that provides a mechanism for securing BGP updates. It involves using digital signatures to ensure the authenticity and integrity of BGP messages. By implementing BGPsec, network operators can prevent route hijacking and route leaks and ensure the stability of the routing system.
9. Filter Your Routes
Filtering your BGP routes can prevent invalid or malicious routes from being propagated throughout your network. You can use prefix lists, route-maps, and Access Control Lists (ACLs) to limit the prefixes you receive and announce based on their source, destination, or other attributes. You can also use route-validation tools, such as RPKI, mentioned above, to verify the ownership and authenticity of the routes.
Pro Tip: Keeping your BGP policies simple and consistent can reduce the chance of errors and misconfigurations that can lead to security incidents. You should avoid complex policies that involve multiple communities, attributes, or variables that are hard to validate or troubleshoot. You should also document your policies and review them regularly to ensure that they align with your business objectives and compliance requirements.
10. Implement BGP Communities
BGP Communities allow you to tag routes with additional information, such as route origin or customer information. It can help you implement security policies across your network, such as filtering out routes from specific customers or networks.
11. Implement BGP Flowspec
BGP Flowspec is a feature that allows you to apply access control policies based on layer 3 and layer 4 packet attributes. It can help prevent DoS attacks, mitigate network congestion, and improve network security.
12. Use Route Refresh Capability
The Route Refresh Capability is a BGP feature that allows you to update routing information without tearing down the BGP session. This can help prevent network instability and reduce the risk of BGP route hijacking attacks.
13. Monitor Your BGP Sessions
Monitoring your BGP sessions can help you detect anomalies, misconfigurations, or attacks in real time. You can use tools such as BGPmon, BGPstream, or NetFlow to analyze your BGP traffic and identify issues such as route leaks, hijacks, or flaps. You can also set up alarms, notifications, or automated responses to alert you of abnormal behavior.
14. Keep Learning
Keeping yourself informed and up-to-date with the latest BGP security trends, technologies, and best practices can help you stay ahead of the game and prevent security incidents. You should participate in industry events, read blogs, join forums, or take courses to expand your knowledge and skills. You should also collaborate with your peers and share your experiences and insights to strengthen the overall security posture of the internet.
Conclusion
In conclusion, securing BGP is an essential task for network engineers and operators to maintain the stability and security of the global Internet infrastructure. The best practices discussed in this article can help network operators to mitigate the risks of BGP security threats such as route hijacking, route leaks, and DDoS attacks. However, it is important to strike a balance between security and the need for efficient routing, as some security measures can impact the performance of the routing system.
Additionally, network operators should consider the impact of security decisions on the wider Internet infrastructure and collaborate with other network operators to implement coordinated security measures. By implementing these best practices and staying up to date with the latest security threats and mitigation techniques, network engineers and operators can help to ensure the stability and security of the global Internet infrastructure.
- pfSense 10G Home Lab Setup: Complete Hardware Guide (2026) - April 1, 2026
- Best Budget Home Lab Setup Under $300 (2026): Complete Starter Stack - March 30, 2026
- Best Modems for Spectrum: Top DOCSIS 3.1 Picks That Actually Work - March 28, 2026