BGP Security Best Practices
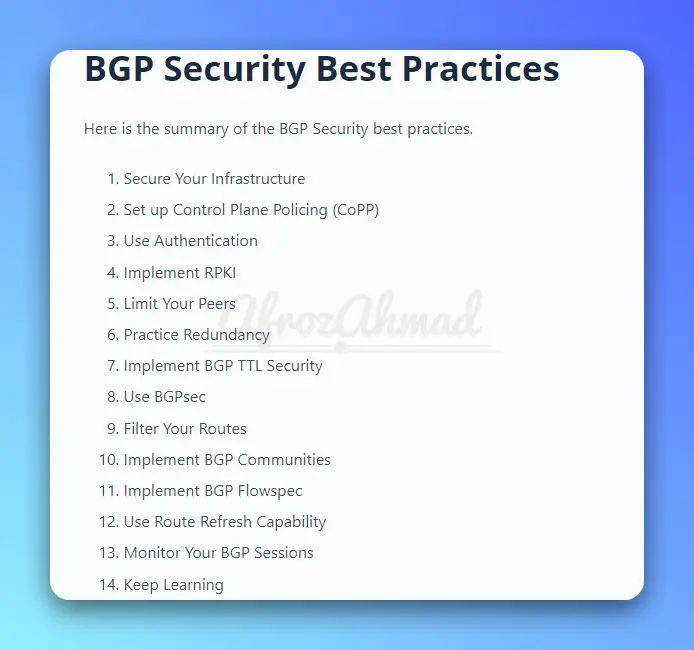
In this article, we will discuss 14 BGP Security best practices. These best practices will help ensure that your network is protected from potential attacks and breaches.
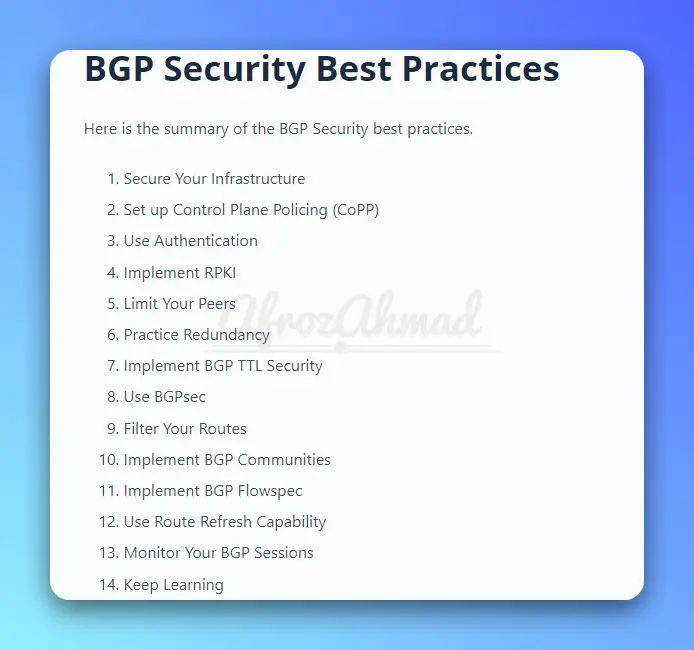
In this article, we will discuss 14 BGP Security best practices. These best practices will help ensure that your network is protected from potential attacks and breaches.
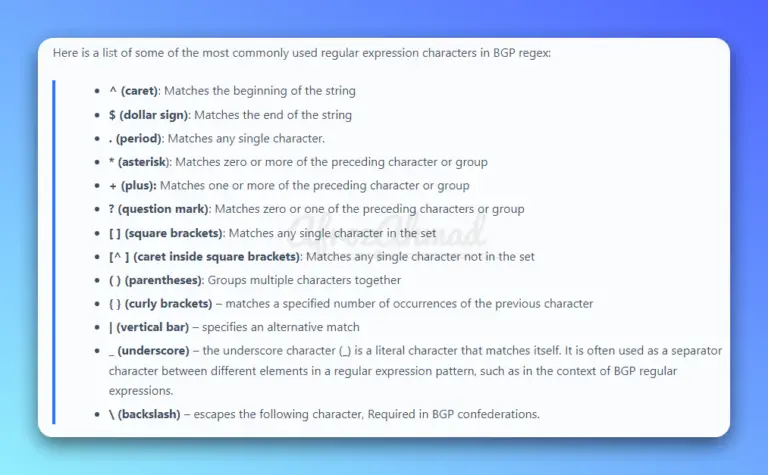
In this comprehensive guide, we will cover everything you need to know about BGP regular expressions, or "regex," and how to use them effectively in your network.
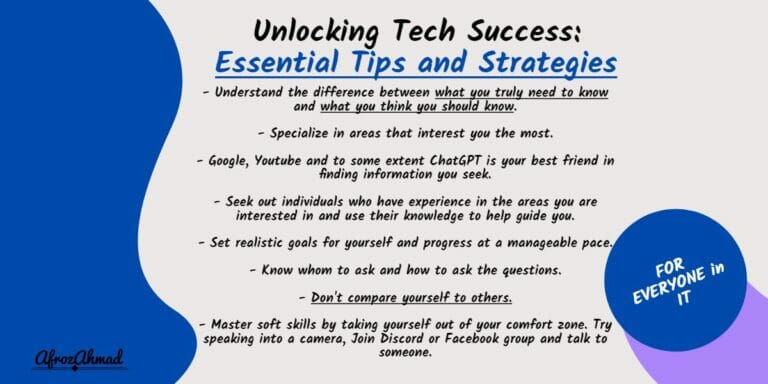
Unlock your tech success as an IT professional with our essential tips and strategies on how to be successful in the IT industry. Learn to navigate the field, find resources, and gain knowledge in a fun and manageable way.
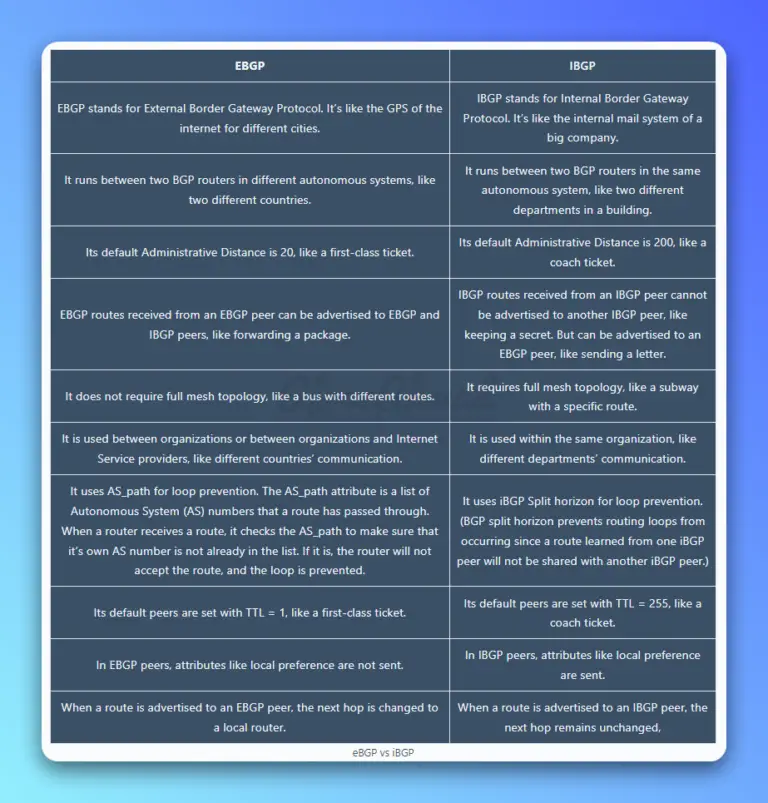
EBGP and IBGP are like your two best friends — one gets you out of the house and lets you explore the world (eBGP), while the other helps keep things running smoothly inside (iBGP). Today, we'll dive into the exciting topic of eBGP vs iBGP.

Network engineering is a challenging and rewarding field that's constantly evolving. By understanding the fundamentals, staying up to date on new technologies and trends, and developing a combination of technical and soft skills, network engineers can stay ahead of the game and navigate the ever-changing landscape of networking.
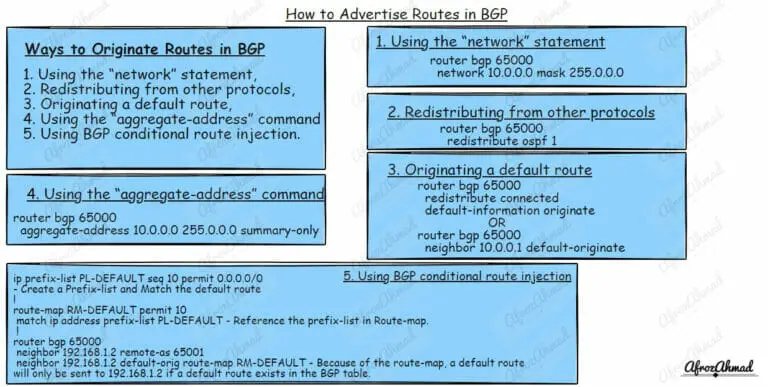
Master the art of BGP route advertisements and control your network like a pro. Learn how to advertise routes in BGP with our practical guide.
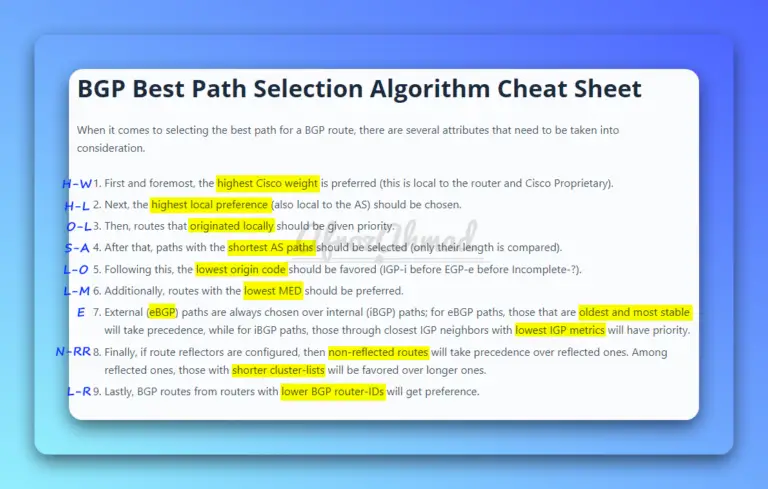
In this article, we'll take an in-depth look at BGP path attributes, the best path selection process, and its cheat sheet.
In this blog post, we'll take a detailed look at the different types of BGP messages and how they are used.
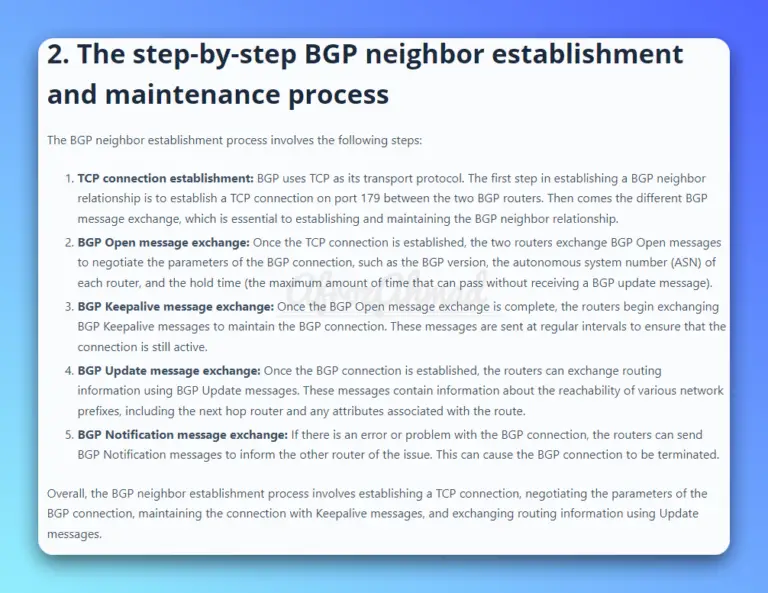
This blog post will explain the BGP Neighborship establishment process.
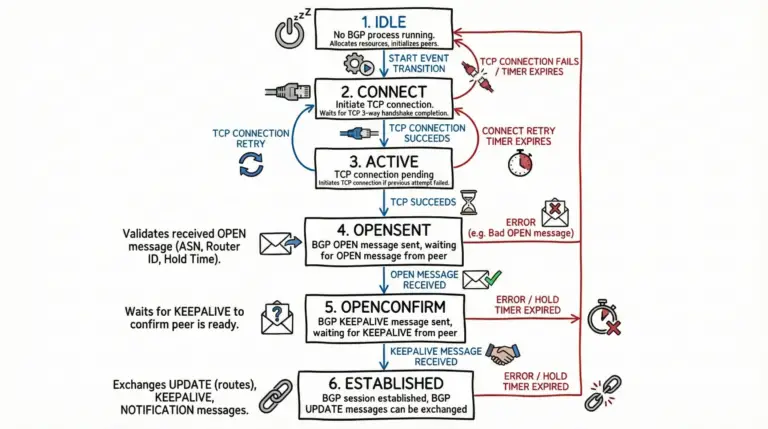
The goal of this article is to give you a full understanding of the six BGP states of a BGP session, which are idle, connect, active, OpenSent, OpenConfirm, and established, as well as how BGP moves between them.