- What is BFD or Bidirectional Forwarding Detection?
- How does BFD Work? – BFD State Machine
- When to Use BFD
- Understanding BFD Packets
- BFD can operate in one of three modes:
- Compatible Protocols with BFD
- Configuring, Verifying, and Testing BFD
- BFD in IPv4 and IPv6 Networks
- Benefits and Drawbacks of BFD
- Real-World Applications of BFD
- Best Practices for BFD Deployment
- The Future of BFD
- Conclusion
If you have experience working with ISPs, you likely understand the important role of BFD in quickly detecting failures and maintaining network resilience. However, if you are not familiar with this technology, don’t worry. In this article, we will delve into the details of BFD, including how it works, its configuration, use cases, best practices, integration with various networking protocols, and more.
What is BFD or Bidirectional Forwarding Detection?
Bidirectional Forwarding Detection (BFD) is a rapid fault detection protocol designed to improve network resilience by identifying failures in forwarding paths within milliseconds.
BFD offloads the responsibility of link failure detection from other protocols, such as Interior Gateway Protocols (IGPs), Border Gateway Protocols (BGP), and others, allowing them to focus on their core functions.
How does BFD Work? – BFD State Machine
A BFD session is established between endpoints over a particular link after negotiating BFD timers and authentication. BFD uses UDP port 3784 and each session is identified by a unique BFD discriminator. The minimum requirements for a BFD session include a minimum transmit interval, a minimum receive interval, and a detection multiplier.
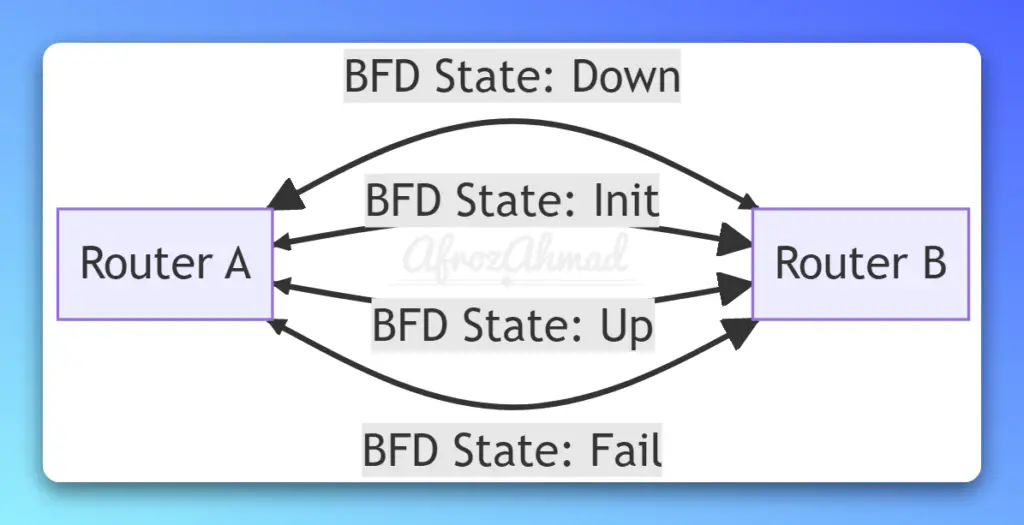
The BFD state machine defines the different states a session can be in such as:
Down – Session has just been established or has just expired due to a timeout.
Init – Waiting for initial BFD packet from the remote system to complete negotiation.
Up – Session has been successfully established, and connectivity is good.
Fail – Connectivity has been lost for the session. Routing protocol needs to act to find an alternate path.
There are additional state machines for demand mode and echo function.
When to Use BFD
- BFD is particularly beneficial in situations where connected neighbors are not directly adjacent at the Layer 1 level. There is no built-in mechanism to notify Router A of a downed link on Router B, such as line protocol.
- BFD can also be employed between tunnel interfaces, ensuring that the routing protocol is promptly informed of any changes in tunnel line protocol status, thereby enabling the termination of the adjacency.
- BFD provides fast BGP neighbor recovery in sub-second timescales, which helps to achieve fast reroute upon interface or node failures in the network. BFD also provides fast failure recovery for static routes and link aggregation groups (LAGs).
- BFD can also operate across multi-hop paths, such as MPLS LSPs, by exchanging BFD packets at each hop. BFD for VCCV is used for MPLS pseudowire status signaling and continuity checking.
Understanding BFD Packets
There are two primary packet types in BFD: Control Packets and Echo Packets.
- Control Packets: Control packets establish BFD peerings and contain essential information, including flags for authentication and timer negotiations. These packets are sent via User Datagram Protocol (UDP) to the bfd-control port (3784) of the far side IP. Since they require processing by the peer, they are transmitted less frequently than BFD echo packets used for sub-second failure detection.
- Echo Packets: BFD echo packets are primarily for local use, with the same source and destination IP addresses. These packets are destined for the UDP bfd-echo port (3785). When received, the router forwards the packet out of the appropriate interface without requiring additional processing. BFD can operate asynchronously by allowing one side to utilize BFD echo detection while the other side maintains a BFD neighbor relationship through control packets.
BFD can operate in one of three modes:
- Asynchronous mode – This is the default mode and uses a slow timer for failure detection and a fast timer for restoration. This provides a good balance of fast reconvergence on failure with minimal false positives.
- Demand mode – Failure detection is triggered by a lack of received BFD packets in response to transmitted BFD packets. This mode is useful for testing a link and reduces the number of packet transmissions.
- Echo mode – Echo packets are looped back through the forwarding path to validate it is working. If no packets are received, a failure is detected. This helps reduce CPU utilization since fewer main BFD packets need to be processed.
Compatible Protocols with BFD
BFD is widely deployed for fast failure detection of network protocols and paths, especially in Service Provider networks. It provides fast sub-second failure detection for OSPF, IS-IS, BGP, static routes, MPLS LSPs, and LAG bundles.
BFD can be used with various protocols, including:
- EIGRP
- OSPF
- IS-IS
- BGP
- HSRP
- Static Routes
- MPLS
- LAG
Configuring, Verifying, and Testing BFD
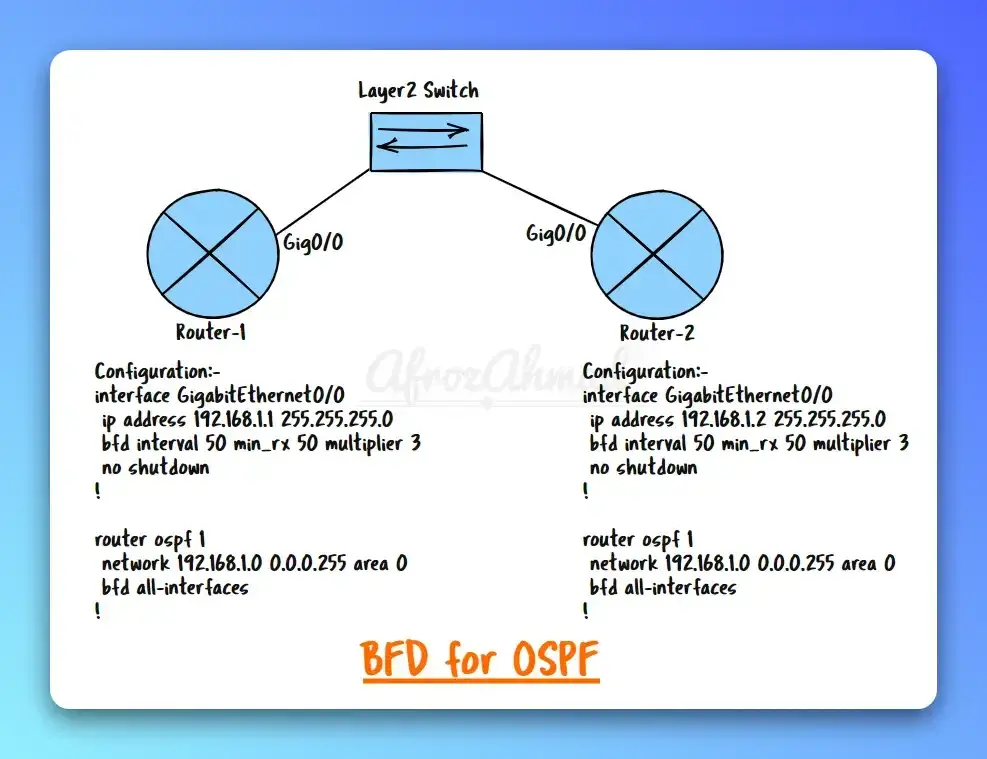
This section demonstrates BFD configuration, verification, and testing using two routers connected via a layer2 switch. The process involves enabling BFD on interfaces, configuring OSPF, and having these protocols register with BFD.
Configuration of Router 1
Enable BFD on the interface by setting the intervals and the mode echo (default). Configure BFD to send hellos every 50ms while accepting a rate of 150ms from a peer and allowing up to three missed hellos before terminating the neighbor-ship.
interface GigabitEthernet0/0
ip address 192.168.1.1 255.255.255.0
bfd interval 50 min_rx 50 multiplier 3
no shutdown
!router ospf 1
network 192.168.1.0 0.0.0.255 area 0
bfd all-interfaces
!Configuration of Router 2
For Router 2, we will use the same type of config.
interface GigabitEthernet0/0
ip address 192.168.1.2 255.255.255.0
bfd interval 50 min_rx 50 multiplier 3
no shutdown
!router ospf 1
network 192.168.1.0 0.0.0.255 area 0
bfd all-interfaces
!Verification and Testing
To verify the configuration, you can use the following commands on both routers:
show bfd neighbors: This command will display the BFD neighbors, session state, and timers.show ip ospf interface GigabitEthernet0/0: This command will display OSPF interface information, including BFD status.show ip ospf neighbor: This command will display OSPF neighbor information, including dead-time, which should be reduced due to BFD.
To test the failure times for each protocol registered with BFD when an interface is brought down, shut down the interface G0/0 on Router 1. On Router 2, within milliseconds of the downed interface, BFD notifies OSPF of the loss and allows them to down their peers.
In a network with multiple paths, BFD ensures that all routes to a peer are removed immediately, and backup routes can be used.
BFD in IPv4 and IPv6 Networks
| BFD | Description |
|---|---|
| BFD for IPv4 | BFD provides a robust mechanism for fault detection and facilitates rapid network convergence in IPv4 networks in the event of failures. |
| BFD for IPv6 | BFD is compatible with IPv6 networks, offering enhanced failure detection capabilities and contributing to the overall stability and performance of next-generation network architectures. |
Benefits and Drawbacks of BFD
BFD offers numerous advantages in network performance and reliability:
- Rapid detection of network failures, improving network resilience
- Offloading the responsibility of link failure detection from other protocols, allowing them to focus on their core functions
- Enhancing the performance of various routing protocols, such as EIGRP, OSPF, BGP, and others
- Reducing the time required to switch to backup routes in case of link failures
BFD Drawbacks –
- BFD can add overhead due to increased packet processing and transmission requirements, so it should only be enabled where fast failure detection is necessary.
Real-World Applications of BFD
| Network Type | BFD Application |
|---|---|
| Data Center Networks | BFD optimizes performance and ensures high availability by monitoring network links, swiftly detecting failures, and maintaining service continuity. |
| Wide Area Networks | BFD monitors the health and performance of links between dispersed locations, enabling rapid detection of failures and swift failover to backup connections. |
| Internet Service Providers | BFD helps maintain the stability of backbone networks and enhances service reliability by detecting failures quickly and rerouting traffic. |
| Enterprise Networks | BFD provides rapid fault detection capabilities to maintain network stability and performance, even in the face of equipment failures or unforeseen issues. |
Best Practices for BFD Deployment
- Proper Timer Configuration: Configuring BFD timers correctly is essential to achieving the desired balance between rapid fault detection and efficient resource utilization. Administrators should carefully consider the unique requirements of their networks when defining timer values.
- Hardware Capability: When enabling BFD, some considerations around timer values, number of sessions supported, echo mode usage, and authentication should be made based on network design and device hardware capabilities. Some network devices also support BFD hardware offloading, which can load-balance BFD packet processing to line cards for better scalability. The BFD control packet format can also be modified for particular hardware match fields.
- Authentication and Security: Implementing robust authentication mechanisms, such as MD5 or SHA-1, can help protect BFD control packet exchanges from tampering or spoofing, ensuring the integrity of the fault detection process.
- Monitoring and Troubleshooting: Effective monitoring and troubleshooting of BFD sessions are crucial to maintaining network stability. Network administrators should establish processes for regularly reviewing BFD logs and other diagnostic information to identify and resolve potential issues.
- Integration with Network Management Systems: Incorporating BFD status information into network management systems can help provide a comprehensive view of network health and performance, enabling administrators to make more informed decisions when addressing network issues.
The Future of BFD
- Emerging Trends: As networking technologies continue to evolve, BFD is likely to play an increasingly prominent role in maintaining network stability and performance, particularly in software-defined and virtualized environments.
- Potential Enhancements: Future enhancements to the BFD protocol may include more efficient resource utilization, improved security mechanisms, and further integration with emerging network technologies, ensuring its continued relevance in the ever-changing landscape of network infrastructure.
Conclusion
In conclusion, Bidirectional Forwarding Detection (BFD) is a lightweight protocol that offers sub-second failure detection between forwarding engines and enhances the reliability of modern network infrastructures. It is increasingly deployed in networks to achieve fast-reroute, sub-50ms link failure detection, and fast PE-CE link failure recovery. When properly tuned, BFD enhances convergence times without excessive false positives.
By understanding its characteristics, use cases, and integration with other networking protocols, you can effectively implement BFD to optimize network performance and ensure service continuity. As networking technologies continue to evolve, BFD is poised to play an increasingly important role in maintaining network stability and addressing the challenges of future network architectures.
- pfSense 10G Home Lab Setup: Complete Hardware Guide (2026) - April 1, 2026
- Best Budget Home Lab Setup Under $300 (2026): Complete Starter Stack - March 30, 2026
- Best Modems for Spectrum: Top DOCSIS 3.1 Picks That Actually Work - March 28, 2026